AmneziaWG
Keywords
| Keyword | Definition |
|---|---|
| 🛡️ AmneziaWG | A fork of WireGuard that randomizes packet headers, sizes, and timing to resist Deep Packet Inspection while keeping the same audited cryptography. It is the protocol that runs on your server. |
| 🚀 AmneziaWG 2.0 | The current major version that uses dynamic header ranges (instead of fixed values), adds data-level padding (S4), and supports Custom Protocol Signature decoy packets for stronger DPI evasion. |
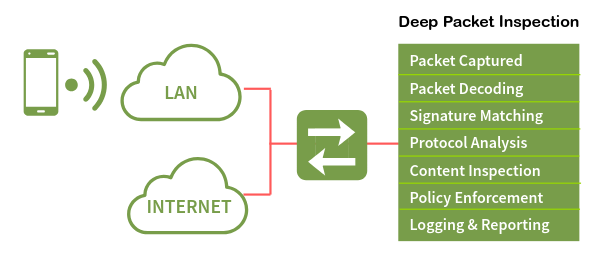
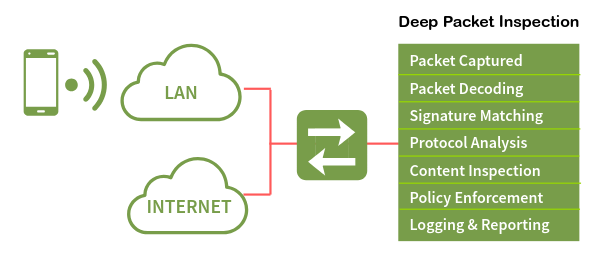
| 🔍 Deep Packet Inspection (DPI) | A network filtering technique used by ISPs and governments to identify and block VPN traffic by analyzing packet headers, sizes, and handshake patterns. AmneziaWG is specifically designed to defeat it. |
| ⚡ WireGuard | A fast, modern VPN protocol with a small codebase and kernel-level performance. It is easily fingerprinted by DPI systems due to its fixed packet structure, which is what AmneziaWG was built to fix. |
| 🏠 Self-hosted VPN | A VPN you deploy and manage on your own server (typically a VPS) rather than subscribing to a commercial provider. You control the keys, config, and infrastructure. |
| 🐧 DKMS (Dynamic Kernel Module Support) | A Linux framework that automatically recompiles kernel modules when the system kernel is updated. The AmneziaWG installer uses DKMS to build the high-performance kernel module. |
| 🎭 Obfuscation | The practice of disguising VPN traffic to look like ordinary internet traffic. AmneziaWG obfuscates at the transport layer by randomizing headers, adding padding, sending decoy packets, and firing junk packets. |
| 🔀 Split tunneling | A routing configuration where only specific traffic (e.g., blocked sites) goes through the VPN while the rest uses your direct connection. Useful in countries with partial censorship. |
| 🖥️ KVM vs LXC | KVM is full virtualization with a dedicated kernel, required for loading custom kernel modules like AmneziaWG. LXC is container-based virtualization that shares the host kernel and cannot load custom modules. |
| 🎪 CPS (Custom Protocol Signature) | An AmneziaWG 2.0 feature that sends decoy packets mimicking other protocols (QUIC, DNS, SIP) before the real handshake, fooling DPI systems into classifying the traffic as normal. |
Self-Host an AmneziaWG VPN Server — Complete Guide

AmneziaWG is a protocol designed to solve a specific problem: how do you get WireGuard’s speed when the networks you’re connecting through actively try to block it? It’s a fork of WireGuard built by the Amnezia VPN team, and it does one thing that the original doesn’t — it randomizes the transport layer so Deep Packet Inspection systems can’t fingerprint it. The encryption underneath stays exactly the same. What changes is how the packets look on the wire.
The broader landscape of VPN obfuscation has been an arms race for years. Tools like Shadowsocks, VLESS+Reality, and OpenVPN with obfs4 all attempt to disguise traffic in different ways — some as proxies, some as full tunnels, some with heavy performance costs. AmneziaWG sits in a specific niche: it’s a full VPN tunnel with WireGuard-level performance and built-in DPI resistance, all in one package. And since it’s open-source, you can self-host it on your own server.
But here’s the problem that makes this necessary. You set up WireGuard. It works perfectly — fast, clean, reliable. Then one day it stops. No error message, no timeout, no connection refused. The packets just vanish. That’s what DPI blocking looks like in practice: your tunnel is still running, your config is still correct, and nothing gets through. This is the reality in Russia (where WireGuard has roughly a 12% success rate), Iran (98% packet loss), and a growing list of countries including China, Egypt, UAE, Turkey, Belarus, Uzbekistan, Kazakhstan, Myanmar, and Pakistan.

Traditional alternatives don’t fully solve this. Shadowsocks is a proxy, not a full VPN tunnel — your DNS and non-TCP traffic still leak. OpenVPN with obfs4 works but carries roughly 25% performance overhead. VLESS+Reality offers strong obfuscation but is proxy-based and complex to configure. AmneziaWG fills the gap: a complete VPN tunnel with WireGuard’s speed and DPI resistance baked in.
This guide walks you through deploying a fully functional AmneziaWG 2.0 server on any KVM VPS in under 15 minutes using a single community installer script. By the end, you’ll have a working VPN tunnel you can connect to from any device. The steps are provider-agnostic — they work on any VPS with root SSH access, whether that’s from AlexHost, AvaHost, or elsewhere. This is written for intermediate tech users who are comfortable with SSH and basic Linux commands.
One clarification before we start: AmneziaWG is the protocol. AmneziaVPN is the client app that connects to it. They’re related but distinct — like TLS is to your browser. You’ll need the app to connect, but the protocol is what runs on your server.
But before we deploy anything, you need to understand what makes AmneziaWG different from WireGuard — and why that difference matters when DPI is watching.
What Is AmneziaWG? (The Mental Model)
WireGuard is elegant by design. It has a small codebase, uses modern cryptography, and runs in the Linux kernel for near-native performance. But that elegance comes with a visibility problem: every WireGuard packet carries the same fixed header structure, the same fixed packet sizes, and the same handshake pattern. To a Deep Packet Inspection system, a WireGuard tunnel has a signature as clear as a barcode. Once a DPI box learns that signature, it can drop every packet without blocking the port or closing the connection.
Think of it this way. WireGuard is like a courier who always wears the same uniform — fast, reliable, and efficient. But anyone watching the road learns to recognize that uniform and can stop the courier at any checkpoint. AmneziaWG is the same courier carrying the same packages, but they change uniforms at every checkpoint. Same person, same cargo, completely different appearance.
The version history matters here. AmneziaWG 1.x introduced custom headers that differed from WireGuard’s fixed values — it helped for a while, but DPI systems adapted. AmneziaWG 2.0, released in late 2025, randomizes everything: headers change per packet, padding varies per message, and decoy packets mimic other protocols before the real handshake begins. There is no universal signature to detect because every AmneziaWG 2.0 server generates its own unique parameter set. Each server speaks its own dialect.
When all obfuscation parameters are set to zero, AmneziaWG behaves identically to WireGuard — it’s fully backward compatible at the protocol level. But with parameters active (which is the default), it becomes something WireGuard cannot be: a fast VPN tunnel that DPI systems struggle to identify.
So how exactly does AmneziaWG scramble its traffic? Let’s look at the four obfuscation layers that make DPI blind — and why they add almost no speed cost.
How AmneziaWG Hides From DPI (Without Losing Speed)
AmneziaWG 2.0 uses four layered obfuscation techniques that work together. Each one targets a different way DPI systems identify VPN traffic. Together, they make every server’s traffic look unique.
Dynamic Headers (H1–H4)
WireGuard uses fixed 32-bit message type identifiers:
- 1 — for initiation
- 2 — for response
- 3 — for cookie reply
- 4 — for data
A DPI box scanning traffic just looks for these values. AmneziaWG 2.0 replaces each fixed value with a random number drawn from a configured range. The initiation header (H1) might be any value between 234567 and 345678. The response header (H2) might be between 3456789 and 4567890. These ranges never overlap — the protocol still needs to distinguish packet types internally — but to an outside observer, there’s no single header value to latch onto. Every packet looks different from the last.
Random Padding (S1–S4)
WireGuard’s initiation packet is always exactly 148 bytes. Its response is always exactly 92 bytes. These fixed sizes are another fingerprint. AmneziaWG adds random padding to each packet type: the initiation becomes 148+S1 bytes, the response becomes 92+S2 bytes, the cookie reply becomes 64+S3 bytes, and every data packet gets S4 bytes of padding. S3 and S4 are new in version 2.0 — and S4 is the most significant addition because it touches every single data packet, making session-wide traffic analysis much harder.
There’s one critical constraint: S1+56 must not equal S2. Since the original size difference between initiation and response is 56 bytes (148−92), if the padding values happened to compensate for exactly that difference, the two padded packets would end up the same size — recreating the fingerprint AmneziaWG is trying to eliminate. The installer’s parameter generator enforces this constraint automatically.
Custom Protocol Signature (I1–I5)
Before the real WireGuard handshake begins, the AmneziaWG client sends up to five decoy packets that mimic other protocols — QUIC, DNS, SIP, or custom byte patterns. The server ignores these packets entirely. It just waits for the real handshake.
- A simple configuration: Sends 128 random bytes <r 128>.
- A sophisticated configuration: Sends bytes that look like a QUIC connection initiation (<b 0xc000000001><r 64><t>), complete with a Unix timestamp.
To a DPI system watching the session start, the first packets look like normal web traffic.
Junk Packets (Jc, Jmin, Jmax)
After the decoy packets, the client fires a configurable number of junk packets — pure noise with random sizes between Jmin and Jmax. These blur the timing and size profile of the session start, making it harder for DPI systems to identify where the real handshake begins.
The Speed Question
There’s a number that’s been circulating online: AmneziaWG has 65% overhead. That figure is real, but it refers to the userspace Go implementation — not the kernel module. The community installer used in this guide builds a DKMS kernel module, and the kernel module adds less than 12% overhead total — closer to 3% in real-world benchmarks. On an uncensored network, you’d see roughly 95 Mbps through WireGuard and 92 Mbps through AmneziaWG 2.0. In a censored network, the comparison is 92 Mbps versus zero.
The following table summarizes the parameters the installer generates automatically:
| Parameter | Generated Range | Example Value |
|---|---|---|
Jc (junk packet count) | 4–8 | 6 |
Jmin (min junk size) | 40–89 | 55 |
Jmax (max junk size) | Jmin+100 to Jmin+500 | 380 |
S1 (init padding) | 15–150 | 72 |
S2 (response padding) | 15–150, S1+56≠S2 | 56 |
S3 (cookie padding) | 8–55 | 32 |
S4 (data padding) | 4–27 | 16 |
H1 (init header range) | uint32 non-overlapping | 234567-345678 |
H2 (response header range) | uint32 non-overlapping | 3456789-4567890 |
H3 (cookie header range) | uint32 non-overlapping | 56789012-67890123 |
H4 (data header range) | uint32 non-overlapping | 456789012-567890123 |
I1 (CPS packet) | <r N> format | <r 128> |
You don’t need to set any of these manually. The installer generates cryptographically random, constraint-valid values every time.
Now that you know how the obfuscation works, let’s see how AmneziaWG stacks up against the alternatives you might be considering.
AmneziaWG vs Alternatives — Quick Decision Guide

| WireGuard | AmneziaWG 2.0 | OpenVPN+obfs4 | Shadowsocks | VLESS+Reality | |
|---|---|---|---|---|---|
| DPI resistance | Low | High | Medium | Medium | Very High |
| Speed overhead | ~4% | <12% (~3% real-world) | ~25% | ~8% | ~10% |
| Full VPN tunnel | Yes | Yes | Yes | No (proxy) | No (proxy) |
| Runs in kernel | Yes | Yes (DKMS) | No | No | No |
| Setup complexity | Low | Low (with installer) | High | Medium | High |
| Transport | UDP | UDP | TCP/UDP | TCP | TCP |
The decision rules are straightforward:
- No DPI in your country? Use plain WireGuard. It’s simpler and has a larger ecosystem.
- Need maximum DPI resistance and OK with a proxy? VLESS+Reality is the strongest option for obfuscation, but it’s not a full tunnel.
- Want both speed and a full tunnel with obfuscation? AmneziaWG 2.0 is the only option that delivers WireGuard-grade performance with real DPI resistance in a complete VPN tunnel.
- Already using OpenVPN+obfs4 and it still works? No urgent need to switch, but AmneziaWG will be noticeably faster.
This article focuses on AmneziaWG because it’s the only protocol that gives you a full tunnel, kernel-level performance, and built-in obfuscation — all configured by a single script.
If AmneziaWG is the right choice for your situation, here’s exactly what you need before we start deploying.
What You’ll Need Before Starting
Before running the installer, make sure your environment meets these requirements:
| Requirement | Detail | Why |
|---|---|---|
| OS | Ubuntu 24.04 LTS (clean install). Ubuntu 25.10 is experimental. Debian 12/13 work but may needcurl pre-installed. | The installer is tested and fully supported on Ubuntu 24.04. |
| VPS specs | 1 vCore, 1 GB RAM, 25 GB storage. Any $3–5/month plan works. | The installer needs ~2 GB disk and ~1 GB RAM during the DKMS build. The running VPN uses negligible resources. |
| Virtualization | KVM (not OpenVZ, not LXC). | AmneziaWG loads a kernel module via DKMS. LXC shares the host kernel and cannot load custom modules. |
| SSH access | Root or sudo user with password/key authentication. | The installer must run as root. |
| SSH port | Default 22, or pre-opened in UFW if using a non-standard port. | If SSH isn’t on port 22 and you don’t pre-open it, the installer’s firewall setup will lock you out. |
| Client app | Amnezia VPN >= 4.8.12.7 (all platforms). | AWG 2.0 parameters are not understood by older clients. The standard WireGuard client does not support AWG at all. |
⚠️ Warning: LXC containers are not supported. If your VPS uses LXC virtualization, the DKMS kernel module build will fail. You must use KVM or bare-metal. Check with your provider if you’re unsure.
⚠️ Warning: If your SSH runs on a non-standard port (anything other than 22), you must open it in UFW before running the installer:
sudo ufw allow YOUR_PORT/tcpReplace
YOUR_PORTwith your actual SSH port. The installer enables UFW with a default-deny policy — if your SSH port isn’t allowed, you’ll be locked out immediately.
💡 Tip: Wait 5–10 minutes after creating your VPS before running the installer. Cloud-init and background initialization processes can conflict with the
apt-getcalls the installer makes.
With your VPS ready and prerequisites confirmed, let’s deploy AmneziaWG 2.0 using the community installer script — the fastest and most transparent method.
Cuvinte cheie
| Cuvânt cheie | Definiție |
|---|---|
| 🛡️ AmneziaWG | Un fork al WireGuard care randomizează antetele pachetelor, dimensiunile și timpii pentru a rezista la Inspecția Profundă a Pachetelor, menținând în același timp aceeași criptografie auditată. Este protocolul care rulează pe serverul tău. |
| 🚀 AmneziaWG 2.0 | Versiunea majoră actuală care folosește intervale dinamice de antete (în loc de valori fixe), adaugă umplutură la nivel de date (S4) și suportă pachete decoy cu semnătură de protocol personalizată pentru o evaziune mai puternică a DPI. |
| 🔍 Inspecția Profundă a Pachetelor (DPI) | O tehnică de filtrare a rețelei utilizată de ISP-uri și guverne pentru a identifica și bloca traficul VPN prin analizarea antetelor pachetelor, dimensiunilor și modelelor de handshake. AmneziaWG este proiectat special pentru a o înfrunta. |
| ⚡ WireGuard | Un protocol VPN rapid și modern cu un cod sursă mic și performanță la nivel de kernel. Este ușor de identificat de sistemele DPI datorită structurii fixe a pachetelor, ceea ce este ceea ce AmneziaWG a fost construit să remedieze. |
| 🏠 VPN auto-găzduit | Un VPN pe care îl desfășori și gestionezi pe propriul server (de obicei un VPS) în loc să te abonezi la un furnizor comercial. Tu controlezi cheile, configurația și infrastructura. |
| 🐧 DKMS (Suport pentru Module de Kernel Dinamic) | Un cadru Linux care recompilă automat modulele de kernel atunci când kernelul sistemului este actualizat. Instalatorul AmneziaWG folosește DKMS pentru a construi modulul de kernel de înaltă performanță. |
| 🎭 Obfuscarea | Practică de a deghiza traficul VPN pentru a arăta ca traficul obișnuit de internet. AmneziaWG obfuscă la nivel de transport prin randomizarea antetelor, adăugarea de umplutură, trimiterea de pachete decoy și generarea de pachete de gunoi. |
| 🔀 Tunneling divizat | O configurație de rutare în care doar un trafic specific (de exemplu, site-uri blocate) trece prin VPN, în timp ce restul folosește conexiunea ta directă. Utilă în țările cu cenzură parțială. |
| 🖥️ KVM vs LXC | KVM este virtualizare completă cu un kernel dedicat, necesar pentru încărcarea modulelor de kernel personalizate precum AmneziaWG. LXC este o virtualizare bazată pe containere care împarte kernelul gazdei și nu poate încărca module personalizate. |
| 🎪 CPS (Semnătură de Protocol Personalizată) | O caracteristică AmneziaWG 2.0 care trimite pachete decoy care imită alte protocoale (QUIC, DNS, SIP) înainte de handshake-ul real, păcălind sistemele DPI să clasifice traficul ca fiind normal. |
Auto-găzduiește un server VPN AmneziaWG — Ghid complet

AmneziaWG este un protocol conceput pentru a rezolva o problemă specifică: cum obții viteza WireGuard atunci când rețelele prin care te conectezi încearcă activ să o blocheze? Este un fork al WireGuard construit de echipa Amnezia VPN și face un lucru pe care originalul nu-l face — randomizează stratul de transport astfel încât sistemele de Inspecție Profundă a Pachetelor să nu-l poată identifica. Criptarea de bază rămâne exact aceeași. Ceea ce se schimbă este modul în care arată pachetele pe fir.
Peisajul mai larg al obfuscării VPN-urilor a fost o cursă înarmată de ani de zile. Instrumente precum Shadowsocks, VLESS+Reality și OpenVPN cu obfs4 încearcă toate să deghizeze traficul în moduri diferite — unele ca proxy-uri, altele ca tuneluri complete, unele cu costuri mari de performanță. AmneziaWG se află într-un nișă specifică: este un tunel VPN complet cu performanță la nivel de WireGuard și rezistență încorporată la DPI, toate într-un singur pachet. Și deoarece este open-source, poți să-l auto-găzduiești pe propriul server.
Dar iată problema care face acest lucru necesar. Ai configurat WireGuard. Funcționează perfect — rapid, curat, fiabil. Apoi, într-o zi, se oprește. Fără mesaj de eroare, fără timeout, fără conexiune refuzată. Pachetele pur și simplu dispar. Așa arată blocarea DPI în practică: tunelul tău încă funcționează, configurația ta este încă corectă și nimic nu trece. Aceasta este realitatea în Rusia (unde WireGuard are aproximativ 12% rată de succes), Iran (98% pierdere de pachete) și o listă tot mai mare de țări, inclusiv China, Egipt, EAU, Turcia, Belarus, Uzbekistan, Kazahstan, Myanmar și Pakistan.

Alternativele tradiționale nu rezolvă complet acest lucru. Shadowsocks este un proxy, nu un tunel VPN complet — DNS-ul tău și traficul non-TCP încă se scurg. OpenVPN cu obfs4 funcționează, dar are un overhead de aproximativ 25% din performanță. VLESS+Reality oferă o obfuscare puternică, dar este bazat pe proxy și complex de configurat. AmneziaWG umple golul: un tunel VPN complet cu viteza WireGuard și rezistența la DPI integrate.
Acest ghid te va ghida prin desfășurarea unui server AmneziaWG 2.0 complet funcțional pe orice VPS KVM în mai puțin de 15 minute folosind un singur script de instalare comunitar. La final, vei avea un tunel VPN funcțional la care te poți conecta de pe orice dispozitiv. Pașii sunt independenți de furnizor — funcționează pe orice VPS cu acces root SSH, fie că este de la AlexHost, AvaHost sau altundeva. Acest text este scris pentru utilizatori tehnici intermediari care sunt confortabili cu SSH și comenzi Linux de bază.
O clarificare înainte de a începe: AmneziaWG este protocolul. AmneziaVPN este aplicația client care se conectează la acesta. Ele sunt legate, dar distincte — la fel cum TLS este pentru browserul tău. Vei avea nevoie de aplicație pentru a te conecta, dar protocolul este ceea ce rulează pe serverul tău.
Dar înainte de a desfășura orice, trebuie să înțelegi ce face AmneziaWG diferit de WireGuard — și de ce această diferență contează atunci când DPI este atent.
Ce este AmneziaWG? (Modelul mental)
WireGuard este elegant prin design. Are un cod sursă mic, folosește criptografie modernă și rulează în kernelul Linux pentru performanță aproape nativă. Dar acea eleganță vine cu o problemă de vizibilitate: fiecare pachet WireGuard poartă aceeași structură fixă de antet, aceleași dimensiuni fixe ale pachetelor și același model de handshake. Pentru un sistem de Inspecție Profundă a Pachetelor, un tunel WireGuard are o semnătură la fel de clară ca un cod de bare. Odată ce o cutie DPI învață acea semnătură, poate elimina fiecare pachet fără a bloca portul sau a închide conexiunea.
Gândește-te la asta în felul următor. WireGuard este ca un curier care poartă întotdeauna aceeași uniformă — rapid, fiabil și eficient. Dar oricine observă drumul învață să recunoască acea uniformă și poate opri curierul la orice punct de control. AmneziaWG este același curier care transportă aceleași pachete, dar își schimbă uniforma la fiecare punct de control. Aceeași persoană, aceeași marfă, apariție complet diferită.
Istoricul versiunilor contează aici. AmneziaWG 1.x a introdus antete personalizate care diferă de valorile fixe ale WireGuard — a ajutat pentru o vreme, dar sistemele DPI s-au adaptat. AmneziaWG 2.0, lansat la sfârșitul anului 2025, randomizează totul: antetele se schimbă pe pachet, umplutura variază pe mesaj, iar pachetele decoy imită alte protocoale înainte de a începe handshake-ul real. Nu există o semnătură universală de detectat pentru că fiecare server AmneziaWG 2.0 generează propriul set de parametri unic. Fiecare server vorbește propriul său dialect.
Când toate parametrii de obfuscare sunt setați la zero, AmneziaWG se comportă identic cu WireGuard — este complet compatibil la nivel de protocol. Dar cu parametrii activi (ceea ce este implicit), devine ceva ce WireGuard nu poate fi: un tunel VPN rapid pe care sistemele DPI se luptă să-l identifice.
Deci, cum exact își scramblează AmneziaWG traficul? Să ne uităm la cele patru straturi de obfuscare care fac DPI orb — și de ce adaugă aproape niciun cost de viteză.
Cum se ascunde AmneziaWG de DPI (fără a pierde viteză)
AmneziaWG 2.0 folosește patru tehnici de obfuscare stratificate care lucrează împreună. Fiecare vizează o modalitate diferită prin care sistemele DPI identifică traficul VPN. Împreună, ele fac ca traficul fiecărui server să arate unic.
Antete dinamice (H1–H4)
WireGuard folosește identificatori de tip de mesaj fixați de 32 de biți:
- 1 — pentru inițiere
- 2 — pentru răspuns
- 3 — pentru răspuns cookie
- 4 — pentru date
O cutie DPI care scanează traficul caută doar aceste valori. AmneziaWG 2.0 înlocuiește fiecare valoare fixă cu un număr aleatoriu extras dintr-un interval configurat. Antetul de inițiere (H1) ar putea fi orice valoare între 234567 și 345678. Antetul de răspuns (H2) ar putea fi între 3456789 și 4567890. Aceste intervale nu se suprapun niciodată — protocolul trebuie să distingă în continuare tipurile de pachete intern — dar pentru un observator extern, nu există o singură valoare de antet la care să se agățe. Fiecare pachet arată diferit de ultimul.
Umplutură aleatoare (S1–S4)
Pachetul de inițiere al WireGuard este întotdeauna exact 148 de biți. Răspunsul său este întotdeauna exact 92 de biți. Aceste dimensiuni fixe sunt o altă amprentă. AmneziaWG adaugă umplutură aleatoare fiecărui tip de pachet: inițierea devine 148+S1 biți, răspunsul devine 92+S2 biți, răspunsul cookie devine 64+S3 biți, iar fiecare pachet de date primește S4 biți de umplutură. S3 și S4 sunt noi în versiunea 2.0 — iar S4 este cea mai semnificativă adăugare deoarece atinge fiecare pachet de date, făcând analiza traficului pe sesiune mult mai dificilă.
Există o constrângere critică: S1+56 nu trebuie să fie egal cu S2. Deoarece diferența de dimensiune originală între inițiere și răspuns este de 56 de biți (148−92), dacă valorile de umplutură se întâmplă să compenseze exact acea diferență, cele două pachete umplute ar ajunge la aceeași dimensiune — recreând amprenta pe care AmneziaWG încearcă să o elimine. Generatorul de parametrii al instalatorului impune automat această constrângere.
Semnătură de Protocol Personalizată (I1–I5)
Înainte de a începe adevăratul handshake WireGuard, clientul AmneziaWG trimite până la cinci pachete decoy care imită alte protocoale — QUIC, DNS, SIP sau modele de biți personalizate. Serverul ignoră complet aceste pachete. Așteaptă doar handshake-ul real.
- O configurare simplă: Trimite 128 de biți aleatori <r 128>.
- O configurare sofisticată: Trimite biți care arată ca o inițiere a conexiunii QUIC (<b 0xc000000001><r 64><t>), complet cu un timestamp Unix.
Pentru un sistem DPI care observă începutul sesiunii, primele pachete arată ca trafic web normal.
Pachete de gunoi (Jc, Jmin, Jmax)
După pachetele decoy, clientul trimite un număr configurabil de pachete de gunoi — zgomot pur cu dimensiuni aleatoare între Jmin și Jmax. Acestea estompează profilul de timp și dimensiune al începutului sesiunii, făcând mai greu pentru sistemele DPI să identifice unde începe adevăratul handshake.
Întrebarea vitezei
Există un număr care circulă online: AmneziaWG are un overhead de 65%. Acea cifră este reală, dar se referă la implementarea utilizatorului Go — nu la modulul de kernel. Instalatorul comunității utilizat în acest ghid construiește un modul de kernel DKMS, iar modulul de kernel adaugă mai puțin de 12% overhead total — mai aproape de 3% în benchmark-uri din lumea reală. Pe o rețea ne-cenzurată, ai vedea aproximativ 95 Mbps prin WireGuard și 92 Mbps prin AmneziaWG 2.0. Pe o rețea cenzurată, comparația este 92 Mbps versus zero.
Tabelul următor rezumă parametrii pe care instalatorul îi generează automat:
| Parametru | Interval generat | Valoare exemplu |
|---|---|---|
Jc (numărul de pachete de gunoi) | 4–8 | 6 |
Jmin (dimensiunea minimă a gunoiului) | 40–89 | 55 |
Jmax (dimensiunea maximă a gunoiului) | Jmin+100 la Jmin+500 | 380 |
S1 (umplutura inițială) | 15–150 | 72 |
S2 (umplutura răspunsului) | 15–150, S1+56≠S2 | 56 |
S3 (umplutura cookie) | 8–55 | 32 |
S4 (umplutura datelor) | 4–27 | 16 |
H1 (intervalul antetului inițial) | uint32 fără suprapunere | 234567-345678 |
H2 (intervalul antetului răspunsului) | uint32 fără suprapunere | 3456789-4567890 |
H3 (intervalul antetului cookie) | uint32 fără suprapunere | 56789012-67890123 |
H4 (intervalul antetului datelor) | uint32 fără suprapunere | 456789012-567890123 |
I1 (pachet CPS) | <r N> format | <r 128> |
Nu trebuie să setezi manual niciunul dintre aceștia. Instalatorul generează valori valide din punct de vedere criptografic, conforme cu constrângerile de fiecare dată.
Acum că știi cum funcționează obfuscarea, să vedem cum se compară AmneziaWG cu alternativele pe care le-ai putea lua în considerare.
AmneziaWG vs Alternative — Ghid rapid de decizie

| WireGuard | AmneziaWG 2.0 | OpenVPN+obfs4 | Shadowsocks | VLESS+Reality | |
|---|---|---|---|---|---|
| Rezistența la DPI | Scăzută | Ridicată | Medie | Medie | Foarte ridicată |
| Overhead de viteză | ~4% | <12% (~3% în lumea reală) | ~25% | ~8% | ~10% |
| Tunel VPN complet | Da | Da | Da | Nu (proxy) | Nu (proxy) |
| Rulează în kernel | Da | Da (DKMS) | Nu | Nu | Nu |
| Complexitatea configurării | Scăzută | Scăzută (cu instalator) | Ridicată | Medie | Ridicată |
| Transport | UDP | UDP | TCP/UDP | TCP | TCP |
Regulile de decizie sunt simple:
- Fără DPI în țara ta? Folosește WireGuard simplu. Este mai simplu și are un ecosistem mai mare.
- Ai nevoie de rezistență maximă la DPI și ești de acord cu un proxy? VLESS+Reality este cea mai puternică opțiune pentru obfuscare, dar nu este un tunel complet.
- Vrei atât viteză, cât și un tunel complet cu obfuscare? AmneziaWG 2.0 este singura opțiune care oferă performanță de nivel WireGuard cu adevărat rezistentă la DPI într-un tunel VPN complet.
- Folosești deja OpenVPN+obfs4 și încă funcționează? Nu este o nevoie urgentă de a schimba, dar AmneziaWG va fi vizibil mai rapid.
Acest articol se concentrează pe AmneziaWG deoarece este singurul protocol care îți oferă un tunel complet, performanță la nivel de kernel și obfuscare încorporată — toate configurate printr-un singur script.
Dacă AmneziaWG este alegerea potrivită pentru situația ta, iată exact ce ai nevoie înainte de a începe desfășurarea.
Ce vei avea nevoie înainte de a începe
Înainte de a rula instalatorul, asigură-te că mediul tău îndeplinește aceste cerințe:
| Cerință | Detaliu | De ce |
|---|---|---|
| OS | Ubuntu 24.04 LTS (instalare curată). Ubuntu 25.10 este experimental. Debian 12/13 funcționează, dar poate necesitacurl pre-installed. | Instalatorul este testat și complet suportat pe Ubuntu 24.04. |
| Specificații VPS | 1 vCore, 1 GB RAM, 25 GB stocare. Orice plan de 3–5 $/lună funcționează. | Instalatorul are nevoie de ~2 GB disk și ~1 GB RAM în timpul construcției DKMS. VPN-ul în execuție folosește resurse neglijabile. |
| Virtualizare | KVM (nu OpenVZ, nu LXC). | AmneziaWG încarcă un modul de kernel prin DKMS. LXC împarte kernelul gazdei și nu poate încărca module personalizate. |
| Acces SSH | Utilizator root sau sudo cu autentificare prin parolă/cheie. | Instalatorul trebuie să ruleze ca root. |
| Port SSH | Implicit 22, sau pre-deschis în UFW dacă folosești un port non-standard. | Dacă SSH nu este pe portul 22 și nu îl deschizi dinainte, configurarea firewall-ului instalatorului te va bloca. |
| Aplicația client | Amnezia VPN >= 4.8.12.7 (toate platformele). | Parametrii AWG 2.0 nu sunt înțeleși de clienții mai vechi. Clientul standard WireGuard nu suportă AWG deloc. |
⚠️ Atenție: Containerele LXC nu sunt suportate. Dacă VPS-ul tău folosește virtualizare LXC, construcția modulului de kernel DKMS va eșua. Trebuie să folosești KVM sau bare-metal. Verifică cu furnizorul tău dacă nu ești sigur.
⚠️ Atenție: Dacă SSH-ul tău rulează pe un port non-standard (orice altceva decât 22), trebuie să-l deschizi în UFW înainte de a rula instalatorul:
sudo ufw allow YOUR_PORT/tcpÎnlocuiește
YOUR_PORTcu portul tău SSH real. Instalatorul activează UFW cu o politică de refuz implicit — dacă portul tău SSH nu este permis, vei fi blocat imediat.
💡 Sfaturi: Așteaptă 5–10 minute după crearea VPS-ului tău înainte de a rula instalatorul. Cloud-init și procesele de inițializare în fundal pot intra în conflict cu apelurile
apt-getpe care le face instalatorul.
Cu VPS-ul tău pregătit și cerințele confirmate, să desfășurăm AmneziaWG 2.0 folosind scriptul de instalare comunitar — cea mai rapidă și transparentă metodă.
Keywords
| Keyword | Definition |
|---|---|
| 🛡️ AmneziaWG | A fork of WireGuard that randomizes packet headers, sizes, and transmission times to counter deep packet inspection while maintaining the same proven cryptography. This is a protocol that runs on your server. |
| 🚀 AmneziaWG 2.0 | The current main version that uses dynamic header ranges (instead of fixed values), adds data-level padding (S4), and supports substitute packets with a custom protocol signature for stronger DPI evasion. |
| 🔍 Deep Packet Inspection (DPI) | A network filtering technique used by ISPs and government entities to identify and block VPN traffic by analyzing packet headers, sizes, and handshake patterns. AmneziaWG is specifically designed to counter this. |
| ⚡ WireGuard | A fast, modern VPN protocol with a small codebase and kernel-level performance. It is easily identifiable by DPI systems due to its fixed packet structure, which has been addressed in AmneziaWG. |
| 🏠 Self-hosted VPN | A VPN that you deploy and manage on your own server (typically a VPS) rather than subscribing to a commercial provider. You control the keys, configuration, and infrastructure. |
| 🐧 DKMS (Dynamic Kernel Module Support) | A Linux framework that automatically recompiles kernel modules when the system kernel is updated. The AmneziaWG installer uses DKMS to build a high-performance kernel module. |
| 🎭 Obfuscation | The practice of disguising VPN traffic to make it appear as regular internet traffic. AmneziaWG obfuscates at the transport layer by randomizing headers, adding padding, sending substitute packets, and generating junk packets. |
| 🔀 Split tunneling | A routing configuration where only specific traffic (e.g., blocked sites) goes through the VPN while other traffic uses your direct connection. Useful in countries with partial censorship. |
| 🖥️ KVM vs LXC | KVM is full virtualization with a dedicated kernel required for loading custom kernel modules like AmneziaWG. LXC is container virtualization that uses the host’s shared kernel and cannot load custom modules. |
| 🎪 CPS (Custom Protocol Signature) | A feature of AmneziaWG 2.0 that sends substitute packets mimicking other protocols (QUIC, DNS, SIP) before the actual handshake, misleading DPI systems by classifying the traffic as normal. |
Self-Deploying AmneziaWG VPN Server — Complete Guide

AmneziaWG is a protocol designed to solve a specific problem: how to achieve WireGuard speeds when the networks you connect to actively try to block it? It is a fork of WireGuard created by the Amnezia VPN team, and it does what the original does not — it randomizes the transport layer so that deep packet inspection systems cannot identify it. The encryption remains exactly the same. Only the appearance of the packets in the network changes.
The broad landscape of VPN obfuscation has been an arms race over the years. Tools like Shadowsocks, VLESS+Reality, and OpenVPN with obfs4 attempt to disguise traffic in various ways — some as proxies, some as full tunnels, some with high performance costs. AmneziaWG occupies a specific niche: it is a full VPN tunnel with WireGuard-level performance and built-in DPI protection, all in one package. And since it is open-source, you can deploy it on your own server.
But here’s the problem that makes this necessary. You set up WireGuard. It works perfectly — fast, clean, reliable. Then one fine day, it stops. No error message, no timeout, no connection refusal. Packets just disappear. This is what DPI blocking looks like in practice: your tunnel is still operational, your configuration is still correct, and nothing is passing through. This is the reality in Russia (where WireGuard has about a 12% success rate), Iran (98% packet loss), and a growing list of countries including China, Egypt, UAE, Turkey, Belarus, Uzbekistan, Kazakhstan, Myanmar, and Pakistan.

Traditional alternatives do not fully solve this problem. Shadowsocks is a proxy, not a full VPN tunnel — your DNS and non-TCP traffic will still leak. OpenVPN with obfs4 works but has about 25% performance overhead. VLESS+Reality offers strong obfuscation but is proxy-based and complex to set up. AmneziaWG fills the gap: it is a full VPN tunnel with WireGuard-level performance and built-in DPI protection.
This guide will walk you through deploying a fully functional AmneziaWG 2.0 server on any KVM VPS in less than 15 minutes using a single community installer script. By the end, you will have a working VPN tunnel that you can connect to from any device. The steps are provider-agnostic — they work on any VPS with SSH access and root privileges, whether from AvaHost, or another. This is written for users with an intermediate level of technical skill who are comfortable working with SSH and basic Linux commands.
One clarification before we begin: AmneziaWG is a protocol. AmneziaVPN is a client application that connects to it. They are related but distinct — like TLS for your browser. You will need an application to connect, but the protocol is what runs on your server.
But before we deploy anything, you need to understand what makes AmneziaWG different from WireGuard — and why that difference matters when DPI is watching you.
What is AmneziaWG? (Mental Model)
WireGuard is elegant in its design. It has a small codebase, uses modern cryptography, and runs in the Linux kernel for nearly native performance. But this elegance has a visibility problem: every WireGuard packet carries the same fixed header structure, the same fixed packet sizes, and the same handshake pattern. For a deep packet inspection system, the WireGuard tunnel has a signature as clear as a barcode. Once a DPI device learns this signature, it can drop every packet without blocking the port or closing the connection.

Think of it this way. WireGuard is like a courier who always wears the same uniform — fast, reliable, and efficient. But anyone watching the road learns to recognize that uniform and can stop the courier at any checkpoint. AmneziaWG is the same courier carrying the same packages, but he changes his uniform at every checkpoint. The same person, the same cargo, a completely different appearance.
Version history matters. AmneziaWG 1.x introduced custom headers that differed from WireGuard’s fixed values — this helped for a time, but DPI systems adapted. AmneziaWG 2.0, released in late 2025, randomizes everything: headers change from packet to packet, padding varies from message to message, and substitute packets mimic other protocols before the actual handshake begins. There is no universal signature for detection because each AmneziaWG 2.0 server generates its own unique set of parameters. Each server speaks its own dialect.
When all obfuscation parameters are set to zero, AmneziaWG behaves identically to WireGuard — it is fully backward compatible at the protocol level. But with active parameters (which is the default setting), it becomes what WireGuard cannot be: a fast VPN tunnel that DPI systems struggle to identify.
So how exactly does AmneziaWG encrypt its traffic? Let’s look at the four levels of obfuscation that make DPI blind — and why they add almost no speed costs.
How AmneziaWG Hides from DPI (Without Speed Loss)
AmneziaWG 2.0 uses four levels of obfuscation that work together. Each targets a different way that DPI systems identify VPN traffic. Together, they make the traffic of each server unique.
Dynamic Headers (H1–H4)
WireGuard uses fixed 32-bit message type identifiers:
- 1 — for initiation
- 2 — for response
- 3 — for response with cookie
- 4 — for data
A DPI device scanning traffic simply looks for these values. AmneziaWG 2.0 replaces each fixed value with a random number chosen from a specified range. The initiation header (H1) can be any value from 234567 to 345678. The response header (H2) can be from 3456789 to 4567890. These ranges never overlap — the protocol still needs to distinguish packet types internally — but for an outside observer, there is no single header value to latch onto. Each packet looks different from the previous one.
Random Padding (S1–S4)
The initiation packet of WireGuard is always exactly 148 bytes. Its response is always exactly 92 bytes. These fixed sizes are another fingerprint. AmneziaWG adds random padding to each packet type: initiation becomes 148+S1 bytes, response becomes 92+S2 bytes, response with cookie becomes 64+S3 bytes, and each data packet receives S4 bytes of padding. S3 and S4 are new in version 2.0 — and S4 is the most significant addition, as it affects every single data packet, making session-level traffic analysis much more difficult.
There is one critical constraint: S1+56 must not equal S2. Since the original size difference between initiation and response is 56 bytes (148−92), if the padding values randomly compensate for exactly that difference, two padded packets will end up the same size — recreating the fingerprint that AmneziaWG is trying to eliminate. The installer’s parameter generator automatically ensures this constraint.
Custom Protocol Signature (I1–I5)
Before the actual handshake begins, the AmneziaWG client sends up to five substitute packets that mimic other protocols — QUIC, DNS, SIP, or custom byte patterns. The server completely ignores these packets. It simply waits for the real handshake.
- Simple configuration: Sends 128 random bytes <r 128>.
- Complex configuration: Sends bytes that look like initiating a QUIC connection (<b 0xc000000001><r 64><t>), with a Unix timestamp.
For a DPI system observing the session start, the first packets look like regular web traffic.
Junk Packets (Jc, Jmin, Jmax)
After the substitute packets, the client sends a customizable number of junk packets — pure noise with random sizes from Jmin to Jmax. These packets blur the timing and size profile of the session start, making it harder for DPI systems to identify where the real handshake begins.
Speed Question
There is a number circulating on the internet: AmneziaWG has 65% overhead. This figure is real, but it refers to the user-space Go implementation — not the kernel module. The community installer used in this guide builds a DKMS kernel module, and the kernel module adds less than 12% overhead overall — closer to 3% in real tests. On an uncensored network, you would see about 95 Mbps through WireGuard and 92 Mbps through AmneziaWG 2.0. On a censored network, the comparison is 92 Mbps versus zero.
The following table summarizes the parameters that the installer generates automatically:
| Parameter | Generated Range | Example Value |
|---|---|---|
| Jc (number of junk packets) | 4–8 | 6 |
| Jmin (min. junk size) | 40–89 | 55 |
| Jmax (max. junk size) | Jmin+100 to Jmin+500 | 380 |
| S1 (initiating padding) | 15–150 | 72 |
| S2 (response padding) | 15–150, S1+56≠S2 | 56 |
| S3 (cookie padding) | 8–55 | 32 |
| S4 (data padding) | 4–27 | 16 |
| H1 (initiation header range) | uint32 without overlap | 234567-345678 |
| H2 (response header range) | uint32 without overlap | 3456789-4567890 |
| H3 (cookie header range) | uint32 without overlap | 56789012-67890123 |
| H4 (data header range) | uint32 without overlap | 456789012-567890123 |
| I1 (CPS packet) | <r N> format | <r 128> |
You do not need to set any of these parameters manually. The installer generates cryptographically random values that meet the constraints every time.
Now that you know how obfuscation works, let’s see how AmneziaWG compares to alternatives you might be considering.
AmneziaWG vs Alternatives — Quick Decision-Making Guide

| WireGuard | AmneziaWG 2.0 | OpenVPN+obfs4 | Shadowsocks | VLESS+Reality | |
|---|---|---|---|---|---|
| DPI Resistance | Low | High | Medium | Medium | Very High |
| Speed Overhead | ~4% | <12% (~3% in real conditions) | ~25% | ~8% | ~10% |
| Full VPN Tunnel | Yes | Yes | Yes | No (proxy) | No (proxy) |
| Runs in Kernel | Yes | Yes (DKMS) | No | No | No |
| Setup Complexity | Low | Low (with installer) | High | Medium | High |
| Transport | UDP | UDP | TCP/UDP | TCP | TCP |
The decision-making rules are simple:
- No DPI in your country? Use regular WireGuard. It’s easier and has a broader ecosystem.
- Need maximum DPI protection and don’t mind proxies? VLESS+Reality is the strongest option for obfuscation, but it’s not a full tunnel.
- Want both speed and a full tunnel with obfuscation? AmneziaWG 2.0 is the only option that delivers WireGuard-level performance with real DPI protection in a full VPN tunnel.
- Already using OpenVPN+obfs4 and it’s still working? No urgent need to switch, but AmneziaWG will be noticeably faster.
This article focuses on AmneziaWG because it is the only protocol that provides you with a full tunnel, kernel-level performance, and built-in obfuscation — all set up with a single script.
If AmneziaWG is the right choice for your situation, here’s what you need before starting the deployment.
What You Need Before You Start
Before running the installer, ensure that your environment meets these requirements:
| Requirement | Details | Why |
|---|---|---|
| OS | Ubuntu 24.04 LTS (clean install). Ubuntu 25.10 is experimental. Debian 12/13 works but may require curl pre-installed. | The installer is tested and fully supported on Ubuntu 24.04. |
| VPS Specs | 1 vCore, 1 GB RAM, 25 GB storage. Any plan for $3–5/month is suitable. | The installer requires ~2 GB of disk space and ~1 GB of RAM during DKMS build. The working VPN uses minimal resources. |
| Virtualization | KVM (not OpenVZ, not LXC). | AmneziaWG loads the kernel module via DKMS. LXC uses a shared host kernel and cannot load custom modules. |
| SSH Access | Root or sudo user with password/key authentication. | The installer needs to run as root. |
| SSH Port | Default 22 or pre-opened in UFW if using a non-standard port. | If SSH is not running on port 22 and you haven’t opened it in advance, the installer’s firewall setup will block you. |
| Client Application | Amnezia VPN >= 4.8.12.7 (all platforms). | The AWG 2.0 options are not understood by older clients. The standard WireGuard client does not support AWG at all. |
⚠️ Warning: LXC containers are not supported. If your VPS uses LXC virtualization, the DKMS kernel module build will fail. You must use KVM or bare-metal. Check with your provider if you are unsure.
⚠️ Warning: If your SSH is running on a non-standard port (anything other than 22), you must open it in UFW before running the installer:
sudo ufw allow YOUR_PORT/tcp
Replace YOUR_PORT with your actual SSH port. The installer includes UFW with a default policy — if your SSH port is not allowed, you will be immediately blocked.
💡 Tip: Wait 5–10 minutes after creating your VPS before running the installer. Cloud-init and background initialization processes may conflict with the calls apt-get that the installer makes.
With your VPS ready and prerequisites confirmed, let’s deploy AmneziaWG 2.0 using the community installer script — the fastest and most transparent method.
Method 1 — Deploy with the CLI Installer (Recommended)
This is the primary installation method. You’ll download a version-pinned installer script, run it as root, walk through eight automated steps (with two expected reboots), and end up with a fully configured AmneziaWG 2.0 server. The installer handles everything: package installation, kernel module compilation, firewall configuration, parameter generation, and service startup.
6.1 — Connect to Your VPS via SSH
Open your terminal and connect to your server:
ssh root@<SERVER_IP>
Replace <SERVER_IP> with your VPS’s actual public IP address. If your provider gave you a non-root user, log in with that user and then escalate:
ssh <username>@<SERVER_IP>
sudo -i
You should see the Ubuntu 24.04 welcome banner followed by a root prompt:
Welcome to Ubuntu 24.04 LTS (GNU/Linux 6.8.0-xx-generic x86_64)
...
root@vps:~#
6.2 — Download and Run the Installer
Download the installer script, make it executable, and run it:
wget https://raw.githubusercontent.com/bivlked/amneziawg-installer/v5.8.1/install_amneziawg_en.sh
chmod +x install_amneziawg_en.sh
sudo bash ./install_amneziawg_en.sh
The URL is version-pinned to v5.8.1 — the latest release as of April 2026. This is supply-chain safety: it ensures the downloaded script matches the tested version, even if the repository has been updated since.
The installer begins by checking your system:
============================================
AmneziaWG 2.0 Installer v5.8.1
============================================
Checking system requirements...
OS: Ubuntu 24.04 LTS — OK
Virtualization: KVM — OK
RAM: 1024 MB — OK
Disk: 25 GB free — OK
If any check fails, the installer stops and tells you why. Fix the issue and re-run the command.
6.3 — Walk Through the Installer Prompts
The installer is an eight-step state machine with resume-after-reboot support. It saves its progress to /root/awg/awgsetup_cfg.init, so if the server reboots, you just run the same command again and it picks up where it left off.
Step 0: Initialization — The installer checks your OS, virtualization type, RAM, and disk space. It creates the /root/awg/ working directory and sets up a lock file to prevent parallel runs.
Step 1: System Update & Package Installation — The installer runs apt-get update && apt-get upgrade -y Then installs AmneziaWG, DKMS, Linux headers, UFW, Fail2Ban, QR code generation tools, and other dependencies.
📝 Note: The installer also removes several background services that consume resources on minimal VPS instances: snapd, modemmanager, networkd-dispatcher, unattended-upgrades, packagekit, lxd-agent-loader, and udisks2. This is intentional and safe for minimal VPN nodes, but may break general-purpose environments.
When Step 1 completes, the installer requests a reboot:
Reboot required. Reboot now? [y/n]:
Type y and press Enter. After the server comes back up, SSH in again and re-run the same command:
sudo bash ./install_amneziawg_en.sh
The script reads its saved state and continues to Step 2 without re-asking any prompts.
Step 2: DKMS Kernel Module Build — The installer compiles the AmneziaWG kernel module against your current kernel and registers it with DKMS for automatic rebuild on future kernel updates:
Step 2: Building AmneziaWG kernel module via DKMS...
Creating symlink /var/lib/dkms/amneziawg/2.0/source -> /usr/src/amneziawg-2.0
DKMS: add completed.
Kernel preparation completed.
Building module:
make -C /lib/modules/6.8.0-xx-generic/build M=/var/lib/dkms/amneziawg/2.0/build modules
DKMS: build completed.
DKMS: install completed.
A second reboot is requested. Type y and press Enter.
📝 Note: Two reboots during installation are normal and expected. The first loads new kernel headers, the second activates the newly built kernel module. The script saves state between reboots — nothing is lost.
After the second reboot, SSH back in and run the installer one more time:
sudo bash ./install_amneziawg_en.sh
Step 3: Post-Reboot Module Verification — The script verifies the kernel module is loaded (lsmod | grep amneziawg). If the DKMS build failed for any reason, it falls back to the userspace Go implementation with a warning about the higher overhead.
Step 4: Firewall Setup — UFW is enabled with a default-deny incoming policy. The installer adds an SSH rate-limiting rule on port 22, opens your VPN port for UDP traffic, and configures routing rules for the awg0 interface.
Step 5: Download Management Scripts — The client management scripts (manage_amneziawg.sh and awg_common.sh) are downloaded to /root/awg/ with owner-only permissions (700). These are also version-pinned to v5.8.1.
Step 6: Interactive Configuration — The installer now asks four questions:
- UDP port (default: 39743, range 1024–65535). The default is a random high port — keep it unless your ISP is known to block high UDP ports.
- Tunnel subnet (default: 10.9.9.1/24). This is your internal VPN network. The server gets .1, clients get .2 through .254, supporting up to 253 clients.
- Disable IPv6 (default: Y). Recommended — disabling IPv6 prevents traffic from leaking outside the tunnel on IPv6 routes.
- Routing mode: Choose 1 for all traffic, 2 for Amnezia List + DNS (recommended), or 3 for custom networks. Mode 2 routes only blocked public IP ranges and DNS through the VPN, keeping your local network access fast and direct.
💡 Tip: The MTU is set to 1280 by default. This is the minimum IPv6 MTU and is critical for mobile and cellular networks. iOS is strict about Path MTU Discovery, and cellular networks often have effective MTU below WireGuard’s default of 1420. Leave this at 1280.
Step 7: Service Start — The installer generates the server configuration at /etc/amnezia/amneziawg/awg0.conf, creates two default client configs (my_phone and my_laptop) at /root/awg/, generates QR codes, and starts the awg-quick@awg0 systemd service.
Step 8: Completion — You’ll see the success message:

The installer generates all AmneziaWG 2.0 obfuscation parameters automatically. You don’t need to touch them. Each server gets a unique set of values — there’s no universal fingerprint for DPI systems to detect.
6.4 — Managing Clients After Installation
The management script at /root/awg/manage_amneziawg.sh handles all client lifecycle operations. Here are the essential commands:
Add a new client:
sudo bash /root/awg/manage_amneziawg.sh add my_desktop
This generates a .conf file, QR code, and .vpnuri file for the new client. The server config is hot-reloaded — no service restart needed.
Add a temporary auto-expiring client:
sudo bash /root/awg/manage_amneziawg.sh add guest --expires=7d
A cron job checks every five minutes and automatically removes the client when it expires. The config, keys, and server entry are all cleaned up.
List all clients:
sudo bash /root/awg/manage_amneziawg.sh list
Clients: my_phone (10.9.9.2/32) my_laptop (10.9.9.3/32) my_desktop (10.9.9.4/32) guest (10.9.9.5/32) [expires in 6d 23h]
Add the -v flag for additional details including public keys and creation dates.
Remove a client:
sudo bash /root/awg/manage_amneziawg.sh remove guest
Check full server status:
sudo bash /root/awg/manage_amneziawg.sh check
This shows the service state, open port, all AWG 2.0 parameters, kernel module status, UFW status, and Fail2Ban status in one view.
View traffic statistics per client:
sudo bash /root/awg/manage_amneziawg.sh stats
Client Received Sent Latest handshake ─────────────────────────────────────────────────────────────────── my_phone 1.24 GiB 356.7 MiB 2 minutes ago my_laptop 892.3 MiB 128.4 MiB 15 seconds ago my_desktop 0 B 0 B (none)
Create a backup:
sudo bash /root/awg/manage_amneziawg.sh backup
This creates a compressed archive at /root/awg/backups/ containing your server config, client configs, keys, and expiry data.
📝 Note: The add and remove commands use awg syncconf for hot-reload. The server config updates instantly without restarting the service. Only use restart when changing server-side parameters like the port or MTU.
6.5 — Verify the Server Is Running
Run through these checks to confirm everything is operational:
Check the systemd service:
sudo systemctl status awg-quick@awg0
● awg-quick@awg0.service - AmneziaWG Quick via awg-quick(8) for awg0
Loaded: loaded (/lib/systemd/system/awg-quick@.service; enabled)
Active: active (exited) since Thu 2026-04-09 14:32:01 UTCVerify AmneziaWG status and parameters:
sudo awg show awg0
Verify the firewall:
sudo ufw status verbose
Status: active Default: deny (incoming), allow (outgoing) 22/tcp LIMIT IN Anywhere 39743/udp ALLOW IN Anywhere
Verify Fail2Ban:
sudo fail2ban-client status sshd
Status for the jail: sshd |- Filter | |- Currently failed: 0 | `- Total failed: 0 `- Actions |- Currently banned: 0 `- Banned IP list:
Verify the DKMS kernel module:
dkms status
amneziawg/1.0.0, 6.8.0-110-generic, x86_64: installed
If all five checks pass, your AmneziaWG 2.0 server is running and ready to accept connections.
Your server is running and verified. If you prefer a GUI-driven approach instead of the terminal, here’s the alternative method using the AmneziaVPN app.
Method 2 — Deploy with the AmneziaVPN App (Alternative)
The AmneziaVPN desktop application can auto-install AmneziaWG on your server via SSH. It uses the same underlying installer script as the CLI method, but wraps everything in a guided interface. This is ideal if you want a hands-off installation experience.
- Download AmneziaVPN from amnezia.org/en/downloads. It’s available for Windows, macOS, Linux, Android, and iOS.
- Open the app and click the ➕ (plus icon) or Get Started.
- Select “Self-hosted VPN” from the options presented.
- Enter your server credentials:
- Server IP address (and port if SSH isn’t on 22, e.g., 203.0.113.10:2221)
- SSH username (e.g., root)
- Password or SSH private key
- Choose the installation type:
- Automatic — installs only AmneziaWG (recommended)
- Manual — choose a specific protocol from the list
- Click “Install” — the app connects to your server via SSH and runs the installation automatically. You’ll see a progress indicator.
- After installation, the app creates a ready-to-use VPN connection profile.
Post-installation notes:
- The app installs AmneziaWG with a random port by default. Some ISPs block UDP on high ports. The app recommends changing to a port below 9999 (such as 585 or 1234). To change it: click the gear icon next to the connection → Management tab → change the port number.
- If your server already has Amnezia software installed, click “Skip setup” during connection creation, then use “Check the server for previously installed Amnezia services” in the Management tab.
Here’s how the two methods compare:
| Aspect | CLI Installer | AmneziaVPN App |
|---|---|---|
| Control | Full — you see every step, can customize | Limited — app handles everything |
| Visibility | Transparent — all commands visible | Opaque — runs behind the scenes |
| Flexibility | Custom routing, endpoint, flags | Uses defaults only |
| Ease of use | Requires SSH familiarity | Zero terminal work |
| Management | Full manage_amneziawg.sh suite | App-based management only |
| Best for | Unmanaged VPS, troubleshooting | Quick setup, guided experience |
Whether you used the CLI or the app, your server is ready. Now let’s connect your first device.
Connecting Your First Client
After installation, you have three ways to import the client configuration into the Amnezia VPN app. Pick the one that matched your device.
Method A: QR Code (Mobile)
The installer generated a QR code at /root/awg/my_phone.png. Download it to your computer:
scp root@<SERVER_IP>:/root/awg/my_phone.png .
Open the PNG file on your screen. On your phone, open the Amnezia VPN app, tap “Add VPN” → “Scan QR code”, and point your camera at the QR code on your screen. The connection imports automatically.
Method B: vpn:// URI (Amnezia Client)
Display the compressed URI on your server:
cat /root/awg/my_phone.vpnuri
Copy the entire vpn://… string and send it to yourself — via Telegram, email, or a notes app. On your phone, open the Amnezia VPN app, tap “Add VPN” → “Paste from clipboard”. The configuration imports in one step.
The URI is a zlib-compressed, Base64-encoded version of the full config file. It’s compact and designed for quick sharing.
Method C: .conf File (Desktop/Windows)
Download the configuration file:
scp root@<SERVER_IP>:/root/awg/my_phone.conf .
Open the AmneziaWG for Windows client or the AmneziaVPN desktop app, click “Import tunnel(s) from file”, and select the .conf file.
Verify the Connection
Once connected, verify the tunnel is routing your traffic through the server:
curl ifconfig.me
The output should show your server’s public IP address, not your local one: 203.0.113.1
For more detail, including the server’s geographic location:
curl -s https://ipinfo.io/json
{
"ip": "203.0.113.1",
"city": "Amsterdam",
"region": "North Holland",
"country": "NL",
...
}⚠️ Warning: The standard WireGuard client does not work with AmneziaWG 2.0 configurations. You must use the Amnezia VPN app (version 4.8.12.7 or later) or a native AmneziaWG client (version 2.0.0 or later on Windows/Android/iOS).
⚠️ Warning: If you see “Invalid key: s3” on Windows, your AmneziaWG Windows client is outdated (version below 2.0.0). Update to version 2.0.0+ or switch to the Amnezia VPN app.
💡 Tip: If you’re connected but have no internet, check that your client config has MTU = 1280 in the [Interface] section. This is the most common cause of “handshake succeeds but no traffic” on mobile networks.
Congratulations! Your VPN tunnel is working.
What Next — Extending Your Setup
You now have a DPI-resistant VPN tunnel running on your own server, under your control, with WireGuard-grade speed. The silent packet death that killed your WireGuard connection is no longer a problem — your traffic looks like nothing a DPI system can reliably identify.
Here are the most useful things you can do next:
- Add clients for your family or team — use the management script to generate configs for every device that needs access.
- Configure split tunneling if you don’t need full-tunnel routing — it keeps local traffic fast and reduces bandwidth on your VPS.
- Back up your configs — run the backup command and store the archive somewhere safe. If your server ever needs rebuilding, this is what saves you from starting over.
Configure split tunneling if you don’t need all traffic routed through the VPN. This is especially useful in countries with partial censorship — route only blocked sites through the tunnel and keep local traffic direct:
sudo bash /root/awg/manage_amneziawg.sh modify my_phone AllowedIPs "192.168.1.0/24,10.0.0.0/8"
Change your client DNS if you prefer different resolvers:
sudo bash /root/awg/manage_amneziawg.sh modify my_phone DNS "8.8.8.8,1.0.0.1"
Adjust PersistentKeepalive if you’re on an aggressive NAT setup. The default of 33 seconds maintains the UDP session through NAT — lowering it to 25 can help on networks that drop idle UDP sessions quickly:
sudo bash /root/awg/manage_amneziawg.sh modify my_phone PersistentKeepalive 25
Install on your router for whole-network coverage. AmneziaWG is supported on Keenetic routers via AWG Manager and on ASUS routers running Asuswrt-Merlin via AmneziaWG for Merlin.
Back up your configuration now, before anything changes:
sudo bash /root/awg/manage_amneziawg.sh backup
If you ever need to migrate to a new server, run a fresh install and then:
sudo bash /root/awg/manage_amneziawg.sh restore
sudo bash /root/awg/manage_amneziawg.sh regen
The restore command brings back your configs and keys, and regen updates the client configurations with the new server IP.
For deeper documentation, the official Amnezia docs are at docs.amnezia.org and the community is active on Telegram.
Conclusion
After going through the full setup, what stands out about AmneziaWG 2.0 is not just that it works—but why it works reliably where others fail. By preserving the proven cryptographic core of WireGuard while fundamentally changing how traffic looks on the network, it sidesteps the exact weaknesses that Deep Packet Inspection exploits. The result is a setup that feels just as fast and simple as WireGuard in practice, but far more resilient in hostile environments. Once deployed, the value becomes obvious: you’re not just running a VPN—you’re running one that’s built to survive real-world blocking.
If you’re looking for a reliable VPS to host your AmneziaWG server — or need to scale up with additional endpoints for team members — AvaHost provide KVM virtualization with full root access, NVMe storage, and Ubuntu 24.04 support that this setup requires. Their infrastructure is purpose-built for the kind of self-hosted deployments this guide covers.

